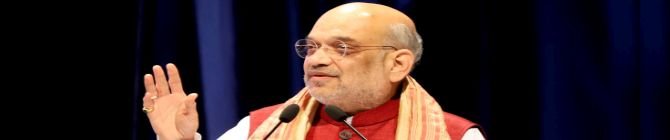
Authorities have been instructed by Union Home Minister Amit Shah to conduct targeted and committed action to apprehend fugitives engaged in smuggling and terrorist activities. This order was given during the opening of the two-day National Security Strategies conference, which was conducted in a hybrid format and involved about 800 officers from all over India.
Shah urged for a reevaluated strategy to disrupt domestic nodes of the terror-criminal nexus and emphasized the need to improve interagency communication between federal and state law enforcement authorities.
A review of terror financing methods with a mandate to uncover terror modules by analyzing financial irregularities was one of Shah’s main points. He also emphasized how crucial it is for police operations to solely use domestic technology.
The Ministry of Home Affairs was tasked by the conference to establish a forum with stakeholders to develop solutions for combating the threat of encrypted communication apps being illegally used by terror networks.
The conference’s first day was devoted to discussing internal ties between external actors that are antagonistic to India’s interests, such as their involvement in the drug trade. Concerns about financing terrorism were discussed alongside the use of technology for crowd control and island security.
Planned topics for the second day were counterterrorism, left-wing extremism, civil aviation and port security, and methods to combat drug trafficking. The gathering comes after Prime Minister Narendra Modi ordered in 2016 that this strategic conference be held every year, leveraging the knowledge of senior and advanced police personnel along with subject-matter specialists to address significant national security issues.
In order to protect the country from changing security threats, Amit Shah’s directives seek to increase efforts in smuggling and terrorism-related fugitive retrieval, improve agency coordination and intelligence sharing, guarantee technological self-reliance, and fortify multi-stakeholder engagement.